Inoculation is effective against this threat.
There was a new spam run overnight; tempting unsuspecting users with a “photo”:
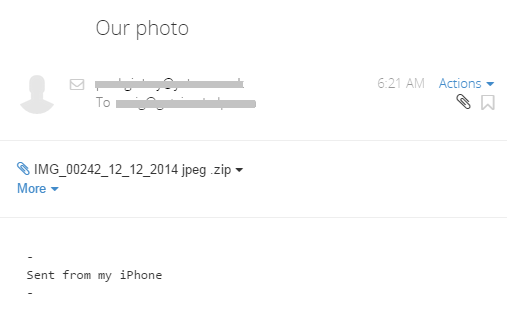
Message: Sent from my iPhone
Attachment: IMG_00242_12_12_2014 jpeg .zip
Inside the attached zip file lurks “IMG_03541_12_12_2014 jpeg .exe”, a malicious downloader trojan, but this is just one of different names. Also seen is the name Sales Receipt_Merchant Report_8740039111_pdf.exe.
When run the threat may crash in some environments, but in others it will install itself in the C:\ProgramData directory as ms???.exe where ? equals a random letter.
A registry run key is created to run the malware on reboot:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run ########## = C:\PROGRA~2\ms???.exe
This process spawns msiexec.exe, which in turn uses Google’s DNS servers (8.8.4.4) to query and subsequently contact the following domains:
- brushes.su
- coverco.net
- maxisurf.net
- micocro.com
Various system policies are set to help conceal the malware:
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\
Advanced “ShowSuperHidden” = 0 - HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\
Explorer “HideSCAHealth” = 0 - HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\
Explorer “TaskbarNoNotification” = 0
The following services are disabled:
- MpsSvc
- SharedAccess
- WinDefend
- wscsvc
- wuauserv
The code contains the following hash, which you can Google to reveal its meaning:
754037e7be8f61cbb1b85ab46c7da77d
About half of the major anti-virus vendors detect at this point (and growing):
https://www.virustotal.com/en/file/b83bafb079be5807ea168553a76a5506abee912fe3e770e5c6a21e9dcf9051d8/analysis/